Introduction
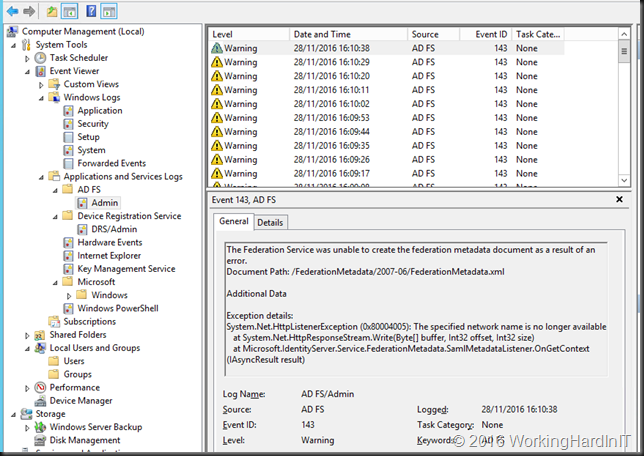
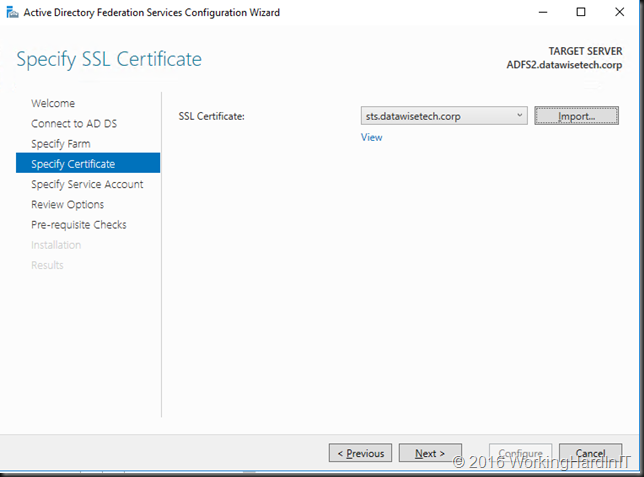
A Windows Server 2016 Farm running had its service communication certificate about to expire so it was time to renew it. Easy you think, get a new cert, get it up and running on all farm member and configure your ADFS farm to use it. Easy enough running Set-AdfsSllCertificate until you get an error.
Set-AdfsSllCertificate: PS0159: the operation is not supported at the current Farm Behavior Level ‘1’. Raise the farm to at least version ‘2’ before retrying.
The cause
At first I was a bit surprised. This is by design and it is mentioned in Managing SSL Certificates in AD FS and WAP in Windows Server 2016. This is typically one of those statement you don’t pay attention to too much until you have the issue.
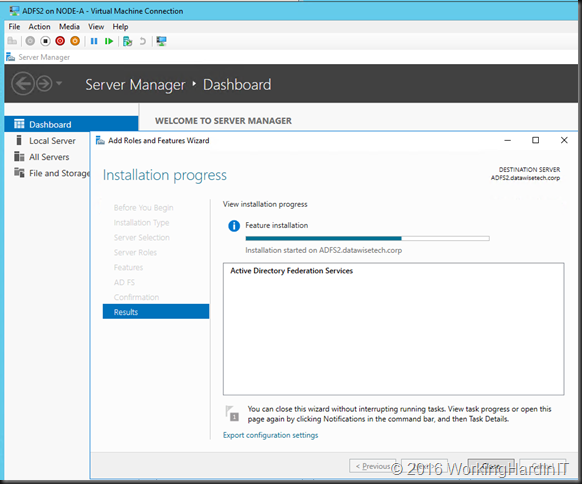
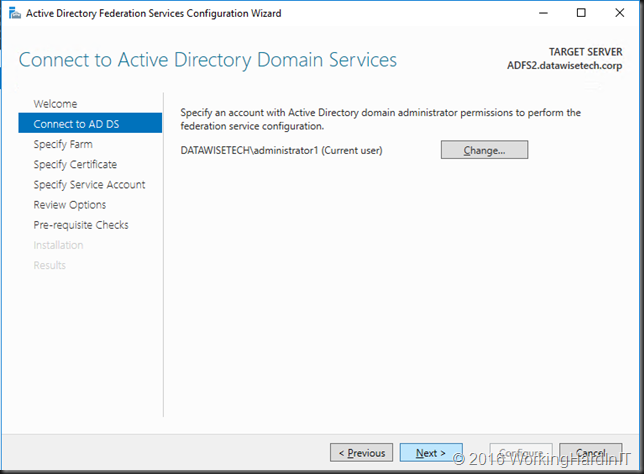
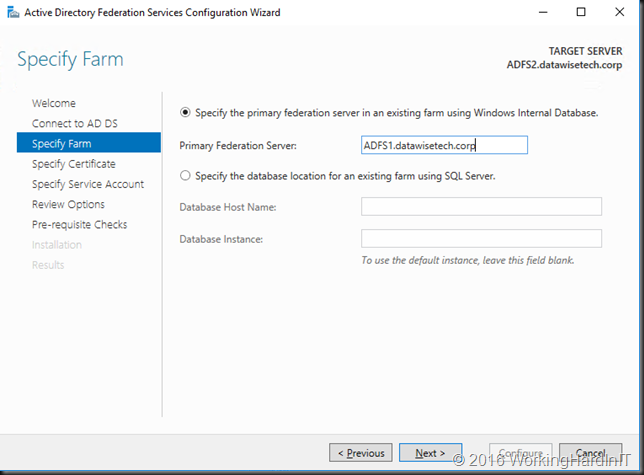
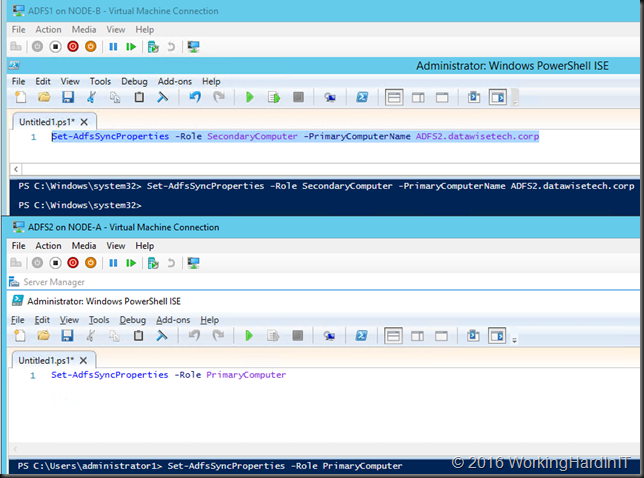
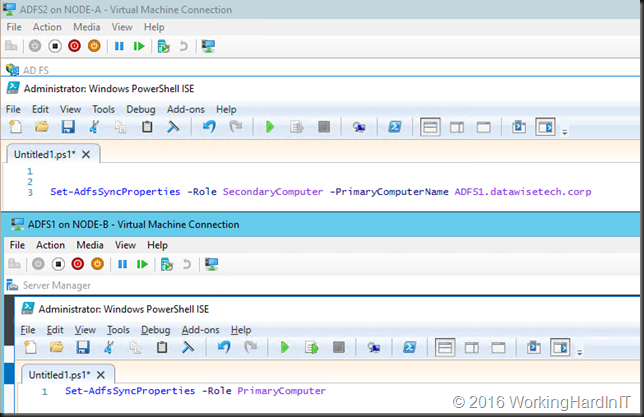
It only occurs with upgraded ADFS Farms (Windows Server 2012 R2 to Windows Server 2016) that have not been raised to the Farm Behavior Level 3. This was the case as the domain was still running Windows Server 2012 R2 DCs and the forest and domain schema updates had not been run yet at the time the ADFS Farm was upgrade from Windows Server 2012 R2 to Windows Server 2016. See Migrate a Windows Server 2012 R2 AD FS farm to a Windows Server 2016 AD FS farm Hence no upgrade was done as without the schema updates you can’t do this and the new functionality this exposes was not available yet anyway. This didn’t cause any issue as the certificate was valid and all operations worked.
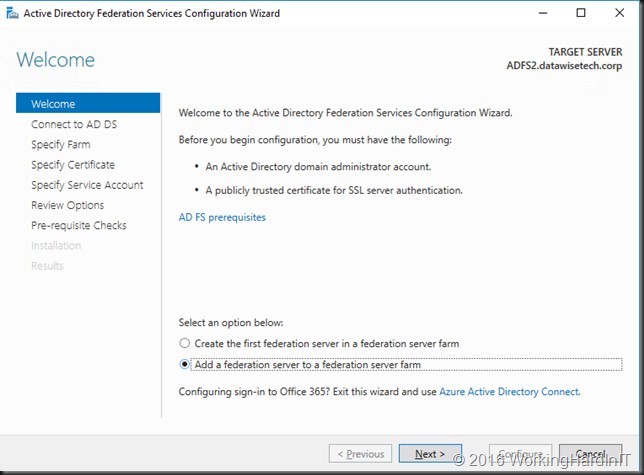
Now, when you install a ADFS farm from scratch on Windows Server 2016 the Farm Behavior Level will read as “3” even it if the domain does not have the forest and domain schemas yet. Basically it sort of lies. But in such an event you won’t have the issue renewing the service communication certificate.
The fix
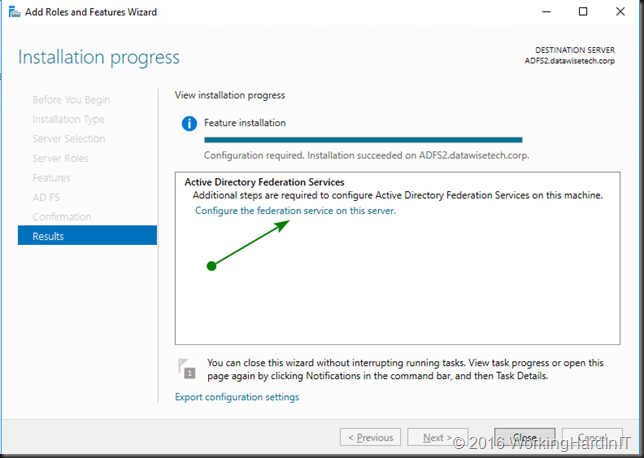
By now the Windows Server 2016 Active Directory schema updates have been run and 80% of all domain controllers are already running Windows Server 2016 at the moment the service communication certificate expired. To be able to replace it we need to do as the error message says: raise the Farm Behavior Level which is now possible as the schema updates are in place.
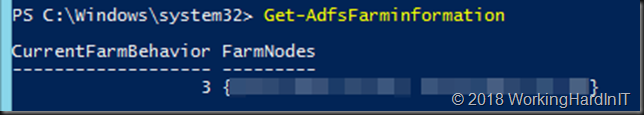
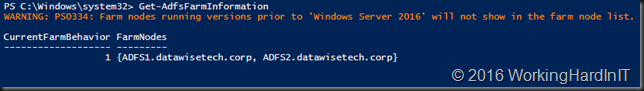
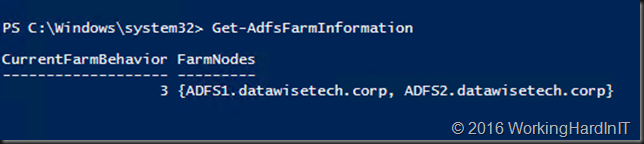
We check it is indeed still at “1”. 
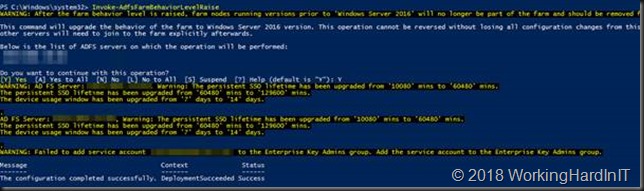
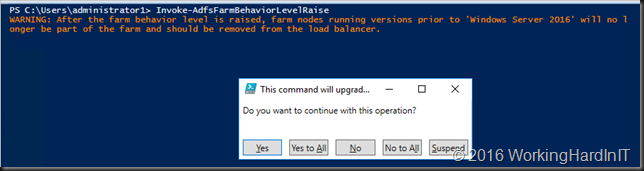
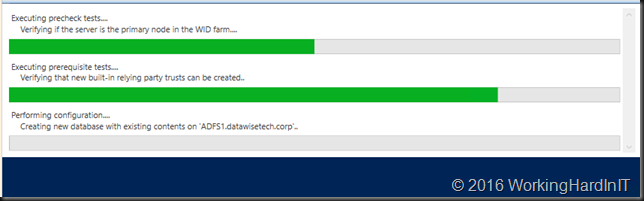
We raise the level. by running Invoke-AdfsFarmBehaviorLevelRaise
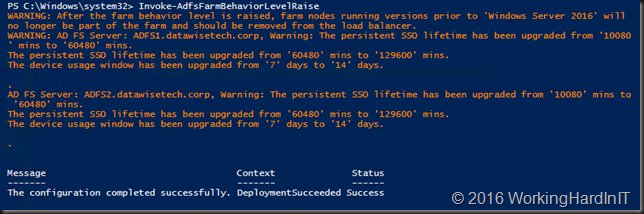
As you cans see it ran successfully. We can check the Farm Behavior Level
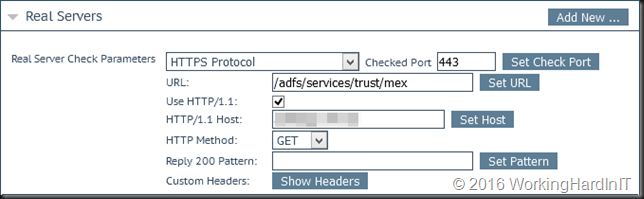
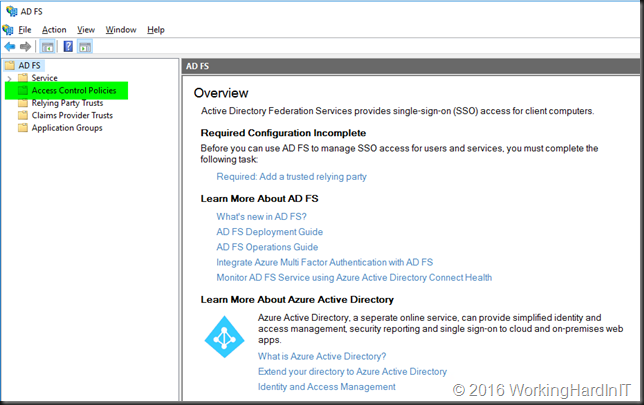
Running Set-AdfsSslCertificate now does work and all is well again.
There you go, no more errors.