Introduction
I was in the process of setting up a new jump server a management station server virtual machine on Windows Server 2016 Hyper-V. The guest was also Windows Server 2016 (desktop install). That station needed to be used to manage some aging Brocade fibre channel switches. With the default setting and links this will give you some headaches and some solution require you to keep older and insecure browser or java versions installed. We’ll show you how to get GUI access to your FC switches without needing to do that so you can manage your Brocade Fibre channel switch with recent Java & browser versions. Well not all of them, but it can be done with IE 11 and Firefox 52.0.1 (at the time of writing).
Another solution is to use the CLI naturally.
Manage Your Brocade Fibre Channel Switch with recent Java & browser versions
It’s OK to use the most recent Java version available. At the moment that I wrote this blog post that was Java 1.8.0.121. I can’t give guarantees other than that, but for now that does work.
Instead of navigating to http or https to just the IP address which will send you to https://x.x..x.x/switchexplorer you need to create a shortcut link to the following: https://10.30.2.2/switchexplorer_installed.html (or http://10.30.2.2/switchexplorer_installed.html if you have not enabled https on your switch).
Like this:
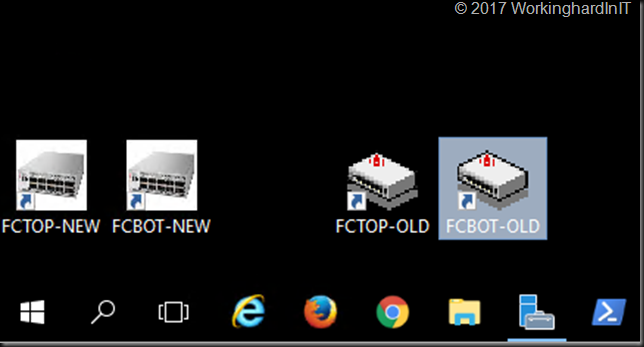
I normally change the icon to the shortcut to indicate it’s pointing to a network device. I actually created some ico files based on an image of brocades Fibre Channel switches that I use for this. I just place then under C:\Programdata\BrocadeFC for safe keeping together with a cop of the short cuts. On the management station, I add them to the desktop for easy access. Below is a screenshot of my Windows 10 or Windows Server 2016 (Desktop Experience) management station.
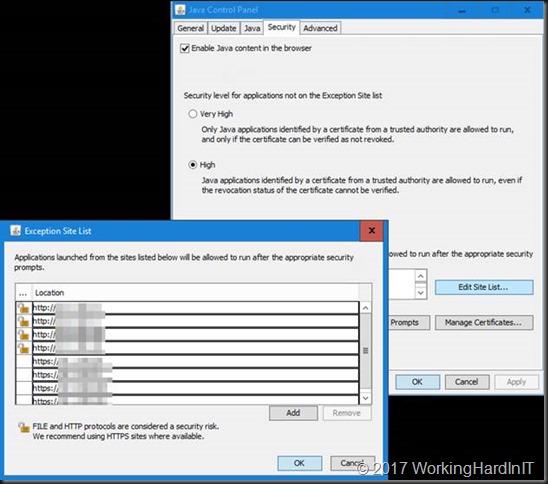
But we’re not there yet. You need to go to Java configuration and select the Security Tab. Make sure Enable Java Content in the browser is enabled. Leave the security at high but don’t forget to add the IP addresses of your Brocade switch to the Exception Site List.
You’ll need to add http or https or both depending on your situation. I think we can all agree we should go for https in this day and age.
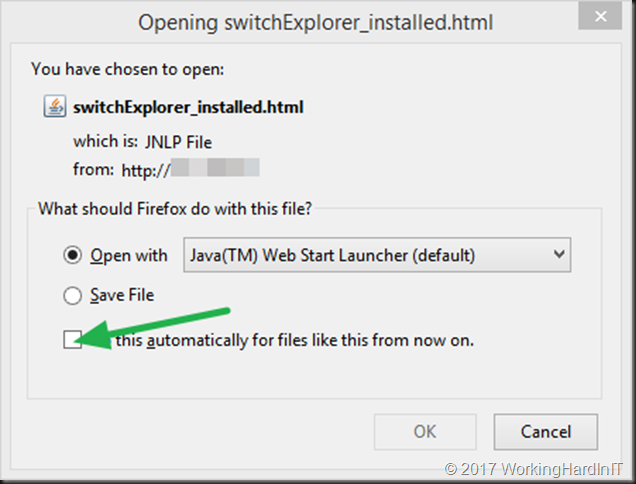
In Firefox when you launch the shortcut you’ll get asked what app to use for opening this file.
Make sure you point it to javaws.exe (in C:\Program Files (x86)\Java\jre1.8.0_121\bin) if that’s not the case.
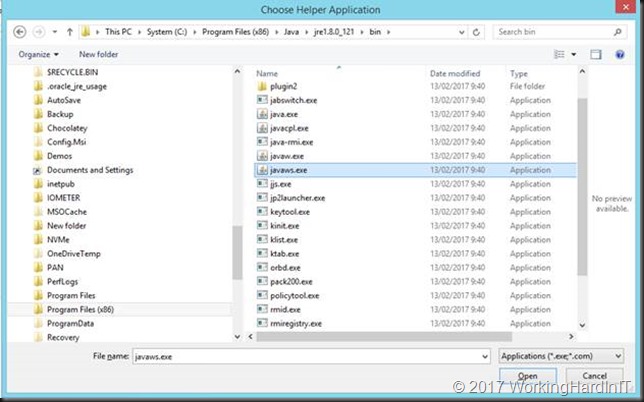 Also, check to “Do this automatically for files like this from now on” for faster access during normal operations.
Also, check to “Do this automatically for files like this from now on” for faster access during normal operations.
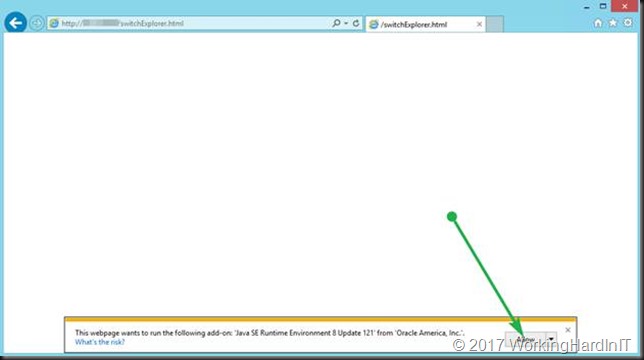
In Internet Explorer allow the add-on “Java SE Runtime Environment 8 Update 121 from Oracle America Inc.” to run.
When it comes to Chrome, this doesn’t’ work anymore. See https://www.java.com/en/download/faq/chrome.xml
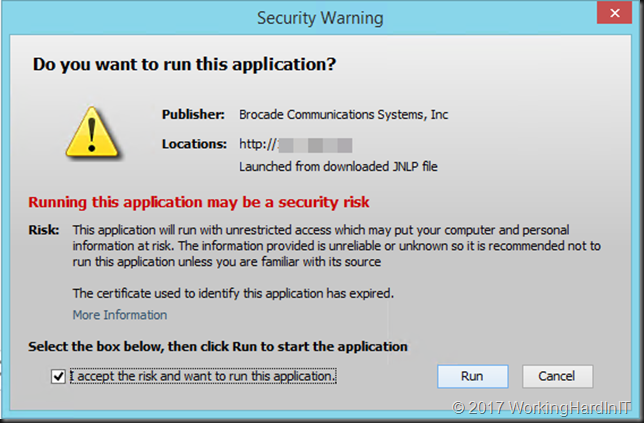
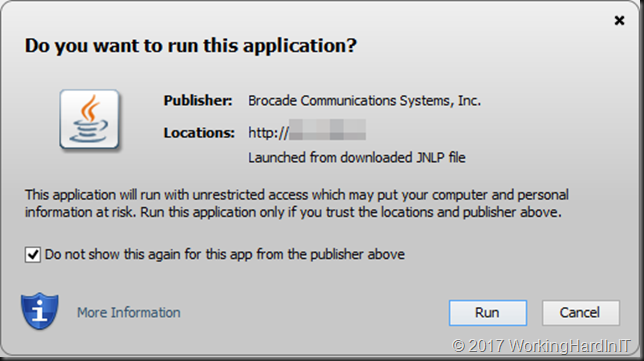
When the application is launched, depending on the age of the fibre channel switch and the version of the firmware you’ll be greeted by a more or less harsh security warning.
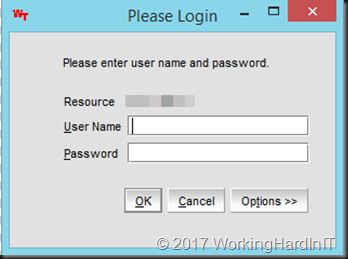
Check the “I accept the risk and want to run this application” or “Do not show this again for this app from the publisher above” depending on the case. This also allows for easy access the next time you launch the shortcut. The app will launch and you’ll be greeted by the login screen.
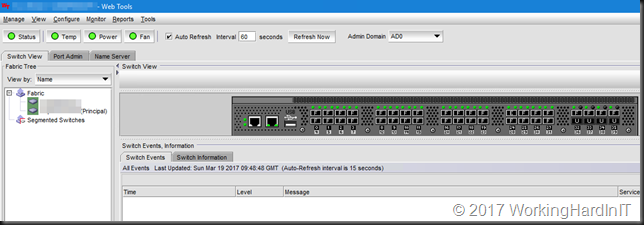
Juts log in and there’s nothing more to it. You can now manage your FC switches from Firefox again.
Hope this helps some of you out there that come across this issue.